There is a critical vulnerability in Ivanti’s MobileIron Core 11.2 version that could allow a malicious actor to gain unauthorized access to restricted functions.
MobileIron core is a product of Ivanti that allows users to securely manage the lifecycle of mobile devices and mobile applications.
It is a combination of MDM (Mobile Device Management), MAM (Mobile Application Management), and MCM (Mobile Content Management).
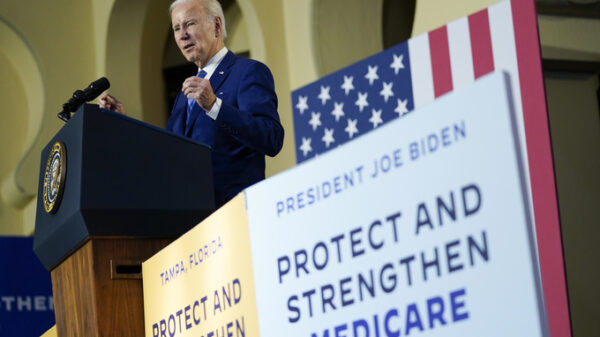
CVE-2023-35082: Remote Unauthenticated API Access Flaw
This authentication bypass vulnerability exists in MobileIron Core versions prior to 11.2. An unauthenticated attacker can exploit this vulnerability and gain access to restricted functionalities or resources of the application.
Ivanti marked the CVSS score for this vulnerability as 10.0 (Critical). However, the official score and vector are yet to be confirmed.
Affected Products & Fixed in Version
MobileIron Core 11.2 versions are out of support on March 15, 2022, as mentioned by Ivanti. Hence, there will be no patches released for this vulnerability.
In order to fix this vulnerability, users are recommended to upgrade to the latest version of Ivanti Endpoint Manager Mobile (EPMM).
Ivanti also credited Stephen Fewer from Rapid7 for reporting this vulnerability. Many product vulnerabilities are identified after they have reached a support period that does not get patches from the product vendor.
Ivanti’s MobileIron Core version below 11.8.1.0 was recently discovered to have a zero-day vulnerability, which enabled remote unauthenticated API access.
This vulnerability was identified as CVE-2023-35078, but Ivanti acted quickly and released security patches to address the issue.
On Friday, the CISA issued a warning about the exploitation of vulnerabilities in Ivanti EPMM (formerly known as MobileIron Core).
It’s important to stay alert and take precautions to protect yourself and your devices from potential threats.
It is a best practice for organizations to keep track of their software versions and upgrade them periodically to avoid exploitation from threat actors.
Source: https://cybersecuritynews.com/ivanti-mobileiron-api-access-flaw/