A new Ducktail phishing campaign is spreading a never-before-seen Windows information-stealing malware written in PHP used to steal Facebook accounts, browser data, and cryptocurrency wallets.
Ducktail phishing campaigns were first revealed by researchers from WithSecure in July 2022, who linked the attacks to Vietnamese hackers.
Those campaigns relied on social engineering attacks through LinkedIn, pushing .NET Core malware masquerading as a PDF document supposedly containing details about a marketing project.
The malware targeted information stored in browsers, focusing on Facebook Business account data, and exfiltrated it to a private Telegram channel that acted as a C2 server. These stolen credentials are then used for financial fraud or to conduct malicious advertising.
Zscaler now reports spotting signs of new activity involving a refreshed Ducktail campaign that uses a PHP script to act as a Windows information-stealing malware.
A PHP information-stealing malware
Ducktail has now replaced the older NET Core information-stealing malware used in previous campaigns with one written in PHP.
Most of the fake lures for this campaign are related to games, subtitle files, adult videos, and cracked MS Office applications. These are hosted in ZIP format on legitimate file hosting services.
When executed, the installation takes place in the background while the victim sees fake ‘Checking Application Compatibility’ pop-ups in the frontend, waiting for a fake application sent by the scammers to install.
The malware will ultimately be extracted to the %LocalAppData%\Packages\PXT folder, which includes the PHP.exe local interpreter, various scripts used to steal information, and supporting tools, as shown below.
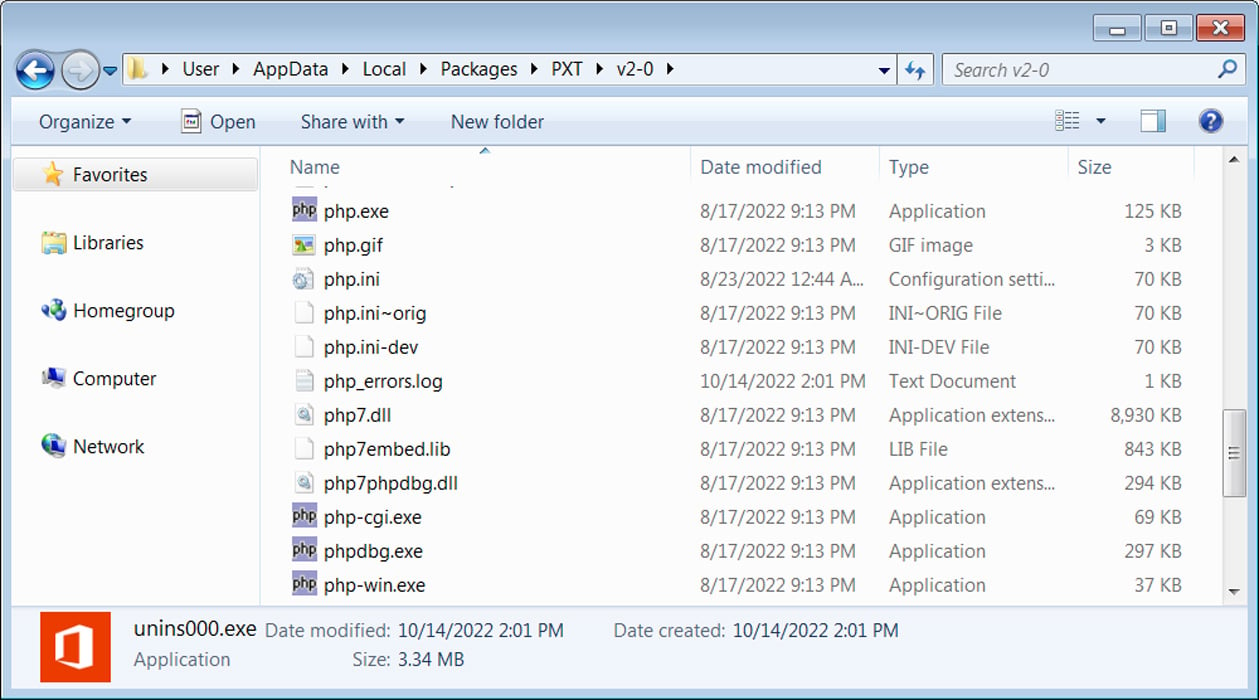
Source: BleepingComputer
The PHP malware achieves persistence by adding scheduled tasks on the host to execute daily and at regular intervals. At the same time, a generated TMP file runs a parallel process to launch the stealer component.
.jpg)
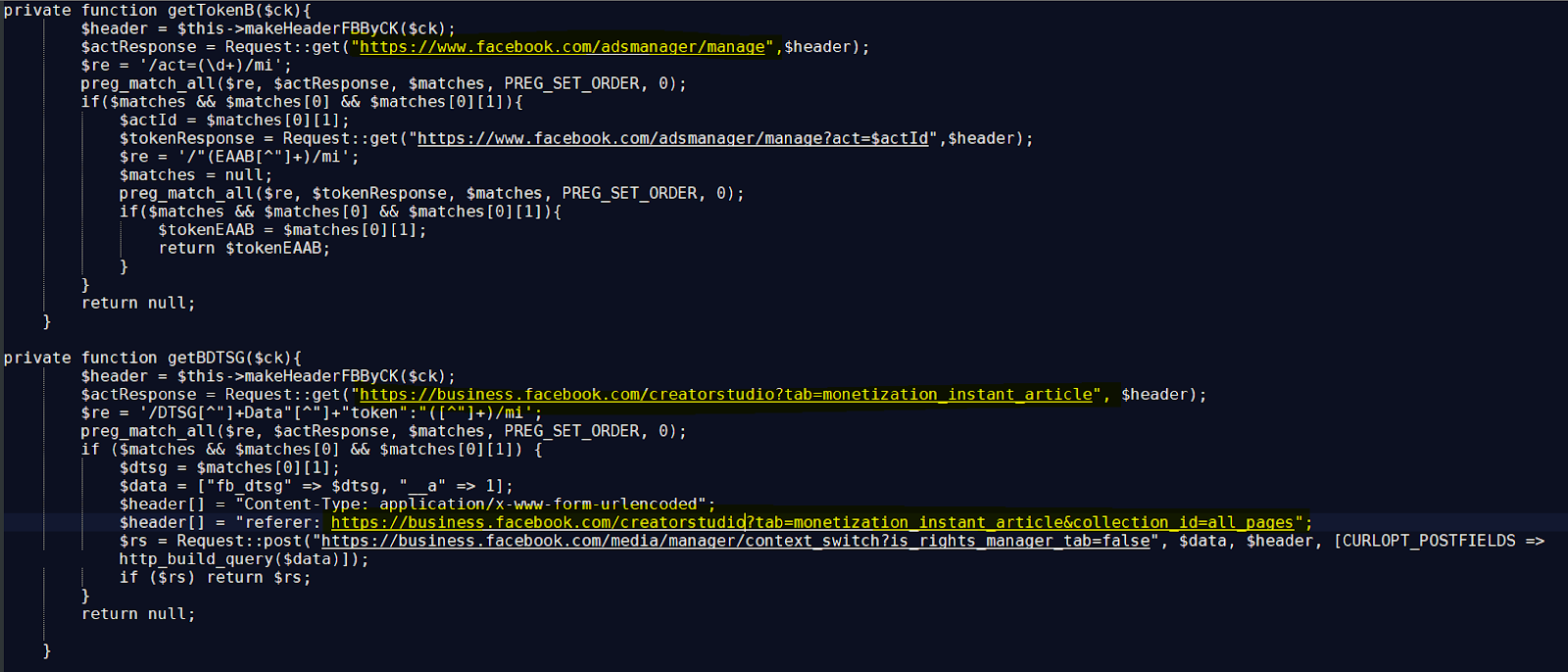
The stealer’s code is an obfuscated (Base64) PHP script, which is deciphered directly on memory without touching the disk, minimizing the chances of being detected.
The targeted data includes extensive Facebook account details, sensitive data stored in browsers, browser cookies, cryptocurrency wallet and account information, and basic system data.
The collected information isn’t exfiltrated to Telegram anymore but instead stored in a JSON website that also hosts account tokens and data required to perform on-device fraud.
Expanding the targeting scope
In the previous campaign, Ducktail targeted employees of organizations working in the financial or marketing department of companies who would likely have permission to create and run advertising campaigns on the social media platform.
The goal was to take control of those accounts and direct payments to their bank accounts or run their own Facebook campaigns to promote Ducktail to more victims.
In the latest campaign, however, Zscaler noticed that the targeting scope has been broadened to include regular Facebook users and to siphon whatever valuable information they may have stored in their accounts.
Still, if the account type is determined to be a business account, the malware will attempt to fetch additional information about payment methods, cycles, amounts spent, owner details, verification status, owned pages, PayPal address, and more.
Ducktail’s evolution and attempt to evade subsequent monitoring by security researchers indicates that the threat actors aim to continue their profitable operations.
Users are advised to be watchful with instant messages on LinkedIn and treat file download requests with extra caution, especially cracked software, game mods, and cheats.